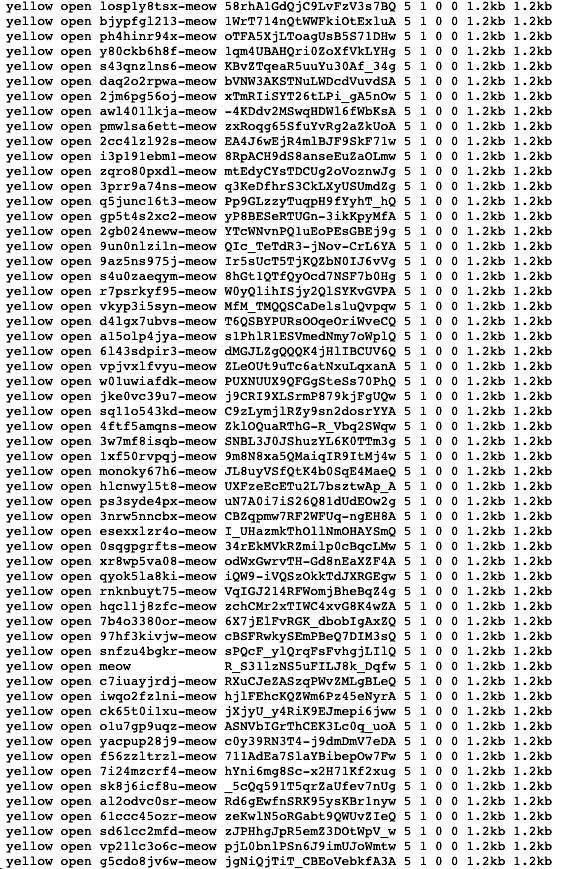
More than 1,000 unsecured databases so far have been permanently deleted in an ongoing attack that leaves the word “meow” as its only calling card, according to Internet searches over the past day.
The attack first came to the attention of researcher Bob Diachenko on Tuesday, when he discovered a database that stored user details of the UFO VPN had been destroyed. UFO VPN had already been in the news that day because the world-readable database exposed a wealth of sensitive user information, including:
- Account passwords in plain text
- VPN session secrets and tokens
- IP addresses of both user devices and the VPN servers they connected to
- Connection timestamps
- Geo-tags
- Device and OS characteristics
- Apparent domains from which advertisements are injected into free users’ Web browsers
Besides amounting to a serious privacy breach, the database was at odds with the Hong Kong-based UFO’s promise to keep no logs. The VPN provider responded by moving the database to a different location but once again failed to secure it properly. Shortly after, the Meow attack wiped it out.
Representatives of UFO didn’t immediately respond to an email seeking comment.
Since then, Meow and a similar attack have destroyed more than 1,000 other databases. At the time this post went live, the Shodan computer search site showed that 987 ElasticSearch and 70 MongoDB instances had been nuked by Meow. A separate, less-malicious attack tagged an additional 616 ElasticSearch, MongoDB, and Cassandra files with the string “university_cybersec_experiment.” The attackers in this case seem to be demonstrating to the database maintainers that the files are vulnerable to being viewed or deleted.


 Loading comments...
Loading comments...